A controversial spy programme developed by senior US operatives on behalf of the UAE for tracking Al-Qaeda terrorists was repurposed by the Gulf monarchy to target political opponents and human rights activists, a Reuters investigation has uncovered.
Amongst the many high-profile victims of the secret counterterror surveillance unit designed to combat the threat of terrorism were the UN, world soccer body FIFA, regional rival Qatar, as well as a number of US companies including Google and Yahoo.
Former US counterterror czar Richard Clarke was the main architect alongside dozens of other American officials of the programme which has raised serious concerns over loopholes that allow Washington’s ex-spies and government insiders to transfer their skills to foreign countries, even ones reputed to have poor human rights track records.
With no check on their power, authoritarian governments like the UAE are able to misuse technology designed to combat serious threats by targeting civilians.
READ: ‘Tel Aviv uses UAE to spy on Qatar, Iran and Hezbollah’
Clarke, a top aide to presidents Bill Clinton and George W Bush, accepted the contract to develop the UAE’s spy programme five years after leaving his senior government position, pushing for more expansive spying powers following the 9/11 terror attack.
The former counter-terrorism official then shopped the same idea to his enthusiastic Gulf partner and employed former National Security Agency (NSA) operatives and other elite American intelligence veterans to help him deliver the multi-million-dollar contract.
In 2008 Clarke helped create a secret unit with an ominous acronym: DREAD, short for Development Research Exploitation and Analysis Department.
By 2011, when the Arab Spring threated to sweep aside every autocrat in the region, the programme designed to combat terrorism was expanded by the UAE to hunt down activists and political opponents. Autocratic rulers of the Gulf state ramped up digital espionage against protesters and others critics of the monarchy.
DREAD targets included activists such as Ahmed Mansoor, a prominent human rights defender, the Reuters investigation found. British activists highlighting human rights concerns in the UAE were also targeted by DREAD operatives.
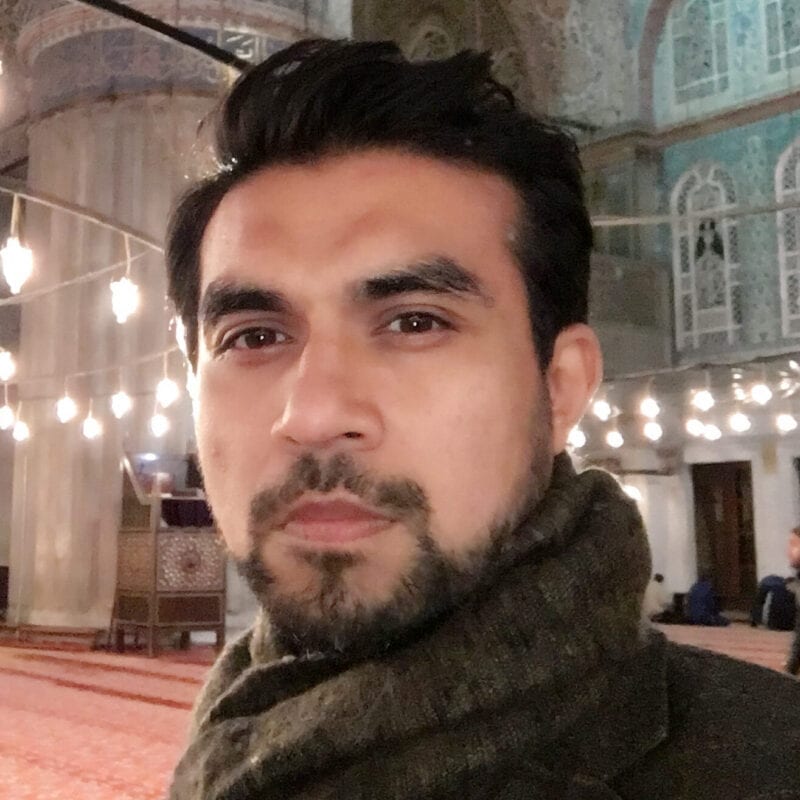
![Political activist Ahmed Mansoor [Nicholas McGeehan/Twitter]](https://i0.wp.com/www.middleeastmonitor.com/wp-content/uploads/2017/03/Ahmed-Mansoor.jpg?resize=920%2C517&ssl=1)
Political activist Ahmed Mansoor [Nicholas McGeehan/Twitter]
Hundreds of government officials and the entire rival foreign governments in the Middle East were targeted through the use of tools developed by former US security agents.
Clarke described details of his work with the UAE and rejected any kind of misconduct. He said that after recommending that the UAE create a cyber surveillance agency, his company, Good Harbor Consulting, was hired to help the country build it. The idea, Clarke said, was to create a unit capable of tracking terrorists claiming that the plan was approved by the US State Department and the NSA, and that Good Harbor followed US law.
The legacy of Clarke’s work with the UAE – which goes as far back as 1991 when as a senior American diplomat he had been sent to the Gulf to seek assistance from regional allies for the war in Iraq – has, however, raised serious questions over the ease with which the technology of war can fall into the wrong hands.
READ: It’s not just Muslims threatened by Israeli groups churning far-right hatred
Through DREAD, dozens of American officials helped the UAE broaden the mission from a narrow focus on active extremist threats to a vast surveillance operation targeting thousands of people around the world perceived as foes by the Emirati government.
The programme’s evolution is seen as an illustration of how Washington’s contractor culture benefits from a system of legal and regulatory loopholes. Increasing numbers of former American intelligence officials are said to be cashing in by working for foreign countries through the transfer of skills including to those with poor human rights track records.
Loopholes have also been exploited to side-step the prohibition against snooping on Americans. DREAD operatives are said to have targeted Google, Hotmail and Yahoo email accounts, despite its proscription. Eventually, the expanding surveillance dragnet swept up American citizens.
Concerns over DREAD’s work with a foreign country was raised by some American recruits, however the programme’s connection to respected national security figures such as Clarke and others led them to conclude the effort was above board. With unease quelled, American officials began to occupy almost every key position in the programme.
They helped locate target accounts, discover their vulnerabilities and cue up cyberattacks. To stay within the bounds of the law, the Americans did not press the button on the ultimate attack, but would often literally stand over the shoulders of the Emiratis who did, 10 former operatives told Reuters.
After the 2011 Arab Spring demonstrations shook the region, Emirati security experts feared their country was next. DREAD’s targets began to shift from counterterrorism to a separate category the UAE termed “national security targets.” The technology assisted in sweeping crackdown against dissidents and others seen as a political threat.
The operations were expanded to human rights groups, UN offices in New York and FIFA executives. The latter was subjected to a ploy designed to steal damaging information about Qatar’s World Cup bid, which could be leaked to embarrass the UAE’s Gulf rival. Allegations that FIFA officials were bribed by Qatar in exchange for granting its World Cup bid surfaced in media reports in 2014.
READ: Why Qatar’s Emir may not attend the Riyadh summit
UAE efforts to undermine its Gulf rival was such that it employed the services of a British Conservative MP and a London-based public relations firm in a campaign to paint Qataris in a negative light and strip the Gulf country of the honour of hosting the 2022 FIFA World Cup. Details of the lengthy campaign were exposed by the New York Times.
Between 2012 and 2015 the surveillance programme became sufficiently resourced such that individual teams were tasked with hacking into entire rival governments, as the programme’s focus shifted from counterterrorism to espionage against geopolitical foes.
Collision was brewing. By 2015 a conflict is said to have emerged between the Emiratis and Americans over the selection of targets. Some US contractors believed that a line had been crossed when US-related entities started being targeted. The UAE team began restricting their US counterparts’ access to surveillance databases, marking some “For Emirati Eyes Only.”
Near the end of 2015, the UAE cancelled its contract and hired a UAE cybersecurity firm, DarkMatter, the commercial arm of the UAE’s cyber intelligence department.
In some cases, DREAD’s surveillance operations preceded the torture of its many targets. In 2017, operatives hacked the emails of Saudi women’s rights activist Loujain Al-Hathloul, after she tried to defy a ban against women driving in Saudi Arabia, a former DREAD operative revealed to Reuters.
Three years earlier, Al-Hathloul, who was studying in the UAE, had been arrested by the Saudis after trying to drive across the border into Saudi Arabia and jailed for 73 days.
The views expressed in this article belong to the author and do not necessarily reflect the editorial policy of Middle East Monitor.